Applies To:
- MOBITEK MobiGATE Model SG-B-4-L / SG-B-8-L series (model having LAN port)
- VCOM version older than 4.5.11
Problem: Windows applications not able to run or the whole PC/server will hang.
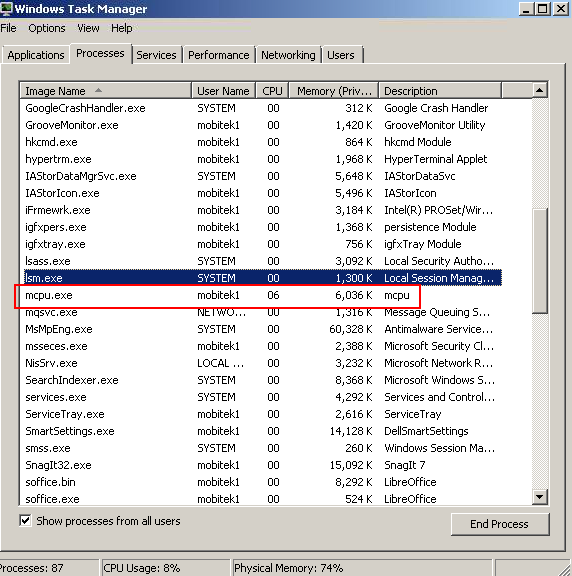
- In “Windows Task Managmer”, “mcpu.exe” will appear everytime VCOM connects to modem in MobiGATE then will disappear:-
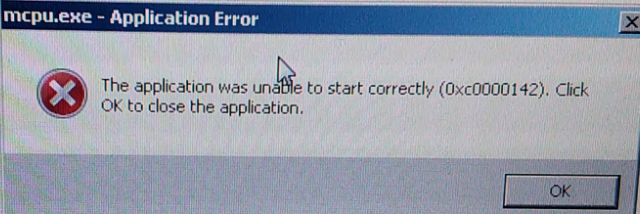
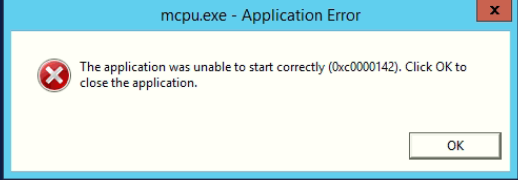
- After running VCOM for few days, Windows will show an error message “mcpu.exe – Application Error : The application was unable to start correctly (0xc0000142)”:-
- “Windows Task Manager” shows high memory usage:-
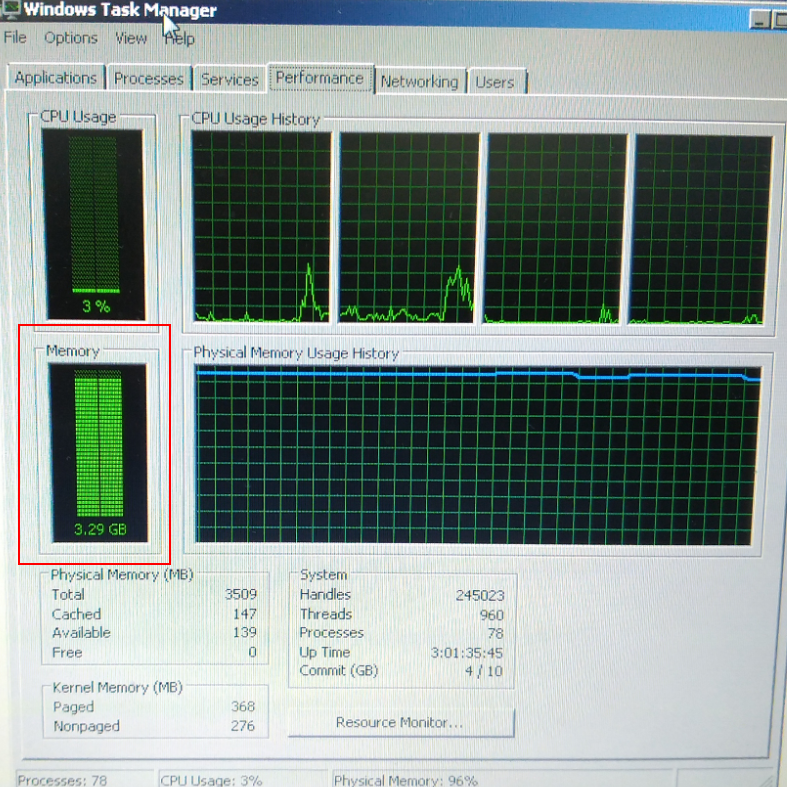
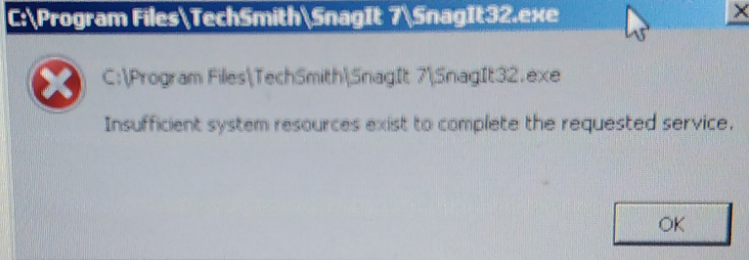
- This will caused other Windows applications not able to run or the whole PC/server will hang:-
Solution: VCOM version older than 4.5.11 has memory leak, causing high memory usage. Therefore, need to install version 4.5.11.




